CHERRY SECURE BOARD 1.0
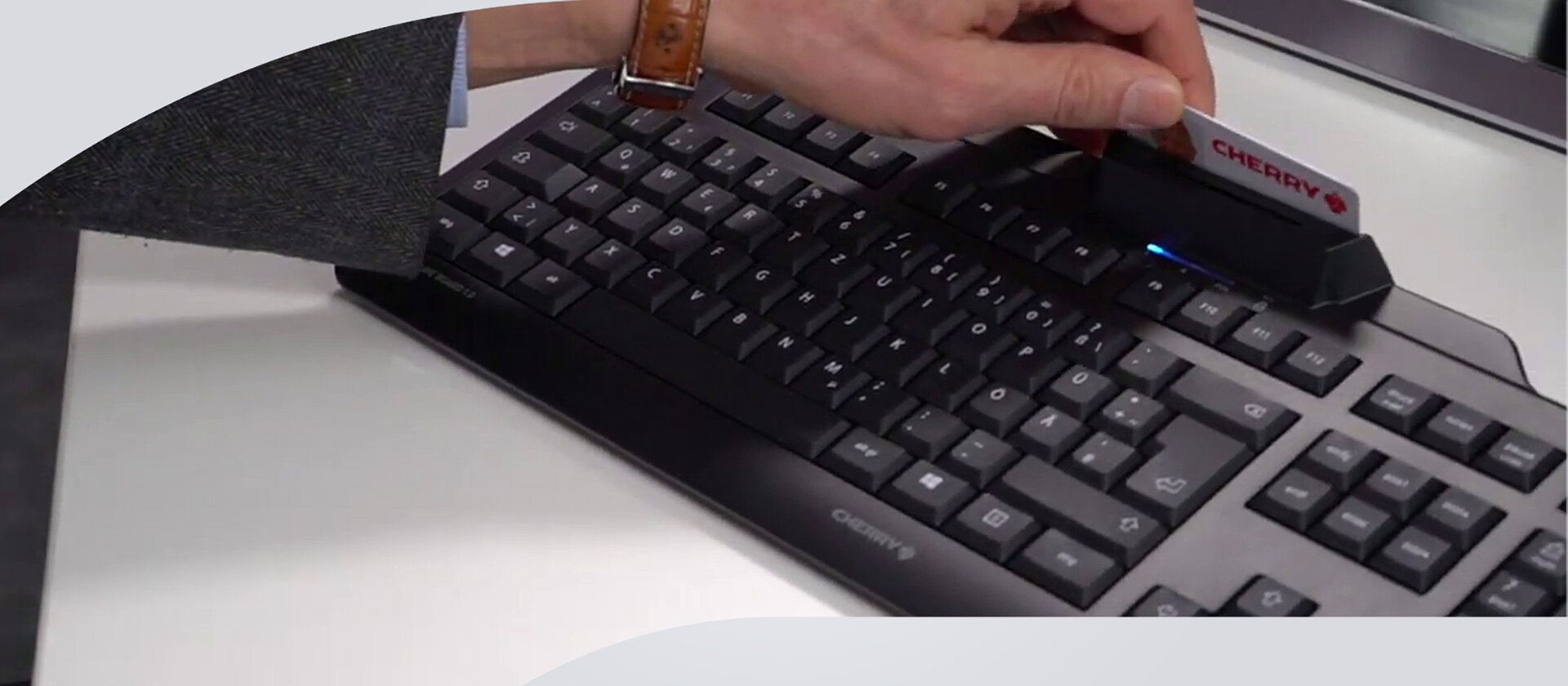
CHERRY SECURE BOARD 1.0 是一款符合人體工學的鍵盤,內建智慧卡與支援 RF/NFC 介面的卡片/標籤讀卡機。 為了提升安全性與資料機密性,該鍵盤可切換至「安全模式」。在此模式下,裝置可透過憑證進行自我驗證,並以加密方式傳輸金鑰。 這使得硬體側錄器無法發揮作用,且由於標準鍵盤通訊通道已被封鎖,「BadUSB」攻擊無法執行。 特別是已內建相關軟體的精簡型終端機(Thin Client),特別適合使用這些功能。
重點特色
- PC/SC 智慧卡讀卡機,支援 CCID
- 通訊協定:T=0、T=1、T=CL
- 可讀寫符合 ISO 7816 與 ISO 14443 A/B 的卡片
- 可讀寫 FIDO2 NFC Token
- 扁平化設計,低高度晶片卡接觸模組
- 符合 FIPS-201 要求
- DE 版本採用 DIN/GS 標準佈局並符合 BGI-650 人體工學指引
- 晶片卡模組可單手操作
- 透過驗證與加密提供安全模式,特別適用於薄型用戶端(Thin Clients)

CHERRY SECURE BOARD 1.0
A central component of modern security concepts is the authentication of users and the authorization of access. Passwords have long since ceased to provide comprehensive access protection - they are all too easily forgotten, changed too infrequently or inadvertently disclosed to third parties due to carelessness.
State of the art, especially in highly sensitive areas, is often two-factor authentication using a smart card. CHERRY follows the “make two into one” approach here and offers a space-saving alternative with the KC 1000 SC and the SECURE BOARD 1.0, in which the card reader is integrated into the keyboard.
In addition, the SECURE BOARD 1.0 also has a contactless card reader located at the back of the keypad. This can also conveniently read RFID and NFC cards or tags contactless This equipment opens up a whole range of applications for the SECURE BOARD 1.0: ID card systems for closed user groups can be used via the keypad and company ID cards, for example, can be read.
Security starts with the input device
We live in a digital world in which everyone is increasingly connected to everything - companies, authorities, institutions with citizens, partners, suppliers and customers. A fundamental element of any security strategy is controlling who has access to the respective IT infrastructure. Cyber security is still often seen as a software problem and assumes that endpoints for trusted applications are secure. However, input devices can also be gateways through which sensitive data input can be tapped before further security measures such as firewalls or virus scanners even take effect. Security keyboards such as the SECURE BOARD 1.0 from CHERRY provide a remedy here.
Insider attacks as one of the greatest sources of danger
Developments such as digitalization and big data and the exponentially growing mountains of data that come with them are arousing desires. Not only from cyber criminals attacking from outside the company, but also from malicious employees or external visitors - insiders who are after information from their employers, customers, partners and government agencies.
Most data breaches are committed by insiders.
According to Verizon's "2024 Data Breach Investigations Report”, insiders are responsible for 70% of incidents in the healthcare industry and 59% in the Public Sector. These breaches involved someone coming in from within the organization.
See how CHERRY products help you close the security breach!
In the past, the insider risk consisted of paper files, for example, which left the company unnoticed and without authorization. Today, the risk is many times higher - digital data, the most valuable asset in any company, often fits on a USB stick or can be removed directly from the company.
In many cases, companies only tackle the problem on the software side. For example, intrusion and prevention systems should help to detect and analyze attacks from the inside at an early stage. In many cases, security starts at the input device.

The human factor: closing the gateway from the inside
Like the environment, the equipment should also be protected according to the security requirements. Possible threats include theft, sabotage, internal hacking or unauthorized access. Cyber criminals - whether malicious employees or external attackers - like to use keyloggers or BadUSB devices for this purpose. Sensitive data, passwords or access codes are tapped by manipulating the input device. This form of sabotage can be prevented comparatively simply but very effectively with the SECURE BOARD 1.0 from CHERRY. With the integrated secure mode, proof of authenticity of the device is certificate-based and key transmission is encrypted. This makes it impossible for hardware keyloggers to intercept sensitive access data and passwords. By blocking the standard keyboard channel, “BadUSB” attacks are also a thing of the past: USB sticks that log on to the system as a keyboard cannot inject uncontrolled input and malicious code.
Defense against malicious code from BadUSB devices
They are small, fit in trouser pockets and the palm of your hand and can transport huge amounts of data: USB sticks. If these mobile data carriers are used for data theft or other malicious actions, the USB sticks, which are neutral in themselves, quickly become a bad USB device.
The problem is that each USB stick has its own controller and firmware in an area that is not visible to the normal user or the operating system. This means that manipulations cannot be detected. For example, the firmware of USB controllers and therefore the BIOS of USB devices can be read and changed. The communication of the USB controller with the host system is completely controlled here.

The manipulated firmware can then turn the USB stick into a network card or a keyboard and redirect or manipulate data traffic, or even inject malicious code into the computer. Unfortunately, existing USB devices can also be reprogrammed in this way and thus subsequently compromised.
The SECURE BOARD from CHERRY provides a remedy here: when the keyboard's secure mode is activated, the standard keyboard channel is blocked. This makes “bad USB” attacks a thing of the past. USB sticks that log on to the system as a keyboard cannot inject any uncontrolled input or malicious code. Well-known thin client manufacturers (e.g. IGEL) already support the use of secure mode and have integrated the necessary software for this. A corresponding solution for Windows will be available soon.
Protect sensitive data (passwords, emails) from hardware keyloggers
A keylogger is a piece of hardware or software that is used to log the user's entries on a computer keyboard and thus monitor or reconstruct them. Keyloggers are used, for example, by crackers, intelligence services or investigative authorities to obtain confidential data such as passwords or PINs. A keylogger can either record all entries or wait for specific keywords, such as access codes, and only then record them in order to save storage space.
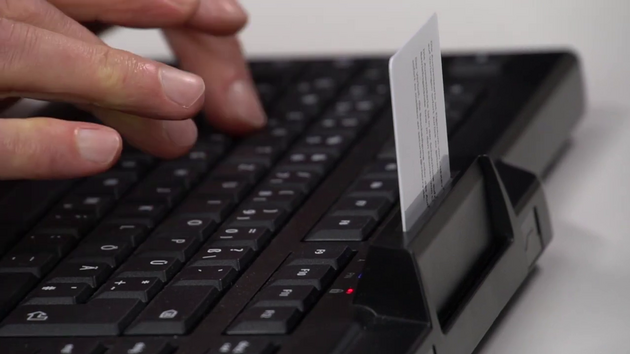
Hardware keyloggers are plugged directly between the keyboard and the computer and can therefore be installed within seconds. Devices that store the spied-out data in an integrated memory (RAM, EPROM, etc.) are then removed again later. The entries logged by them are then read out on another computer. Other techniques send the logged data via networks or wirelessly.
How the CHERRY SECURE BOARD 1.0 protects sensitive data
With the SECURE BOARD 1.0, CHERRY has a solution in its portfolio that effectively eliminates precisely these threats posed by hardware keyloggers: With the secure mode, the device's proof of authenticity is certificate-based and key transmission is encrypted. This makes it impossible for hardware keyloggers to intercept sensitive access data and passwords.
The CHERRY SECURE BOARD 1.0 offers first-class security features and reliable performance, ideal for use in sensitive and demanding work environments.
Further chip card-based applications and advantages of the dual-interface feature can be found here:
屬性
| 保固 | 2年法定保固 |
|---|---|
| 軟體支援 | CHERRY KEYS, PC/SC Diagnose Tool |
| 電纜長度 | 180 cm |
| 鍵帽材質 | ABS |
| 按鍵標示 | 雷射標記 |
| 可調式腳墊 | 集成的 |
| 狀態指示燈 | 在住房 |
| 關鍵技術 | 橡膠圓頂 |
| 總按鍵行程 | 3 mm |
| 預行程 | 2,5 mm |
| 操作力 (cN) | 70 cN |
| Service life per key (in million strokes) | 10 Mio. 操作 |
| 切換特性 | standard |
| Keyboard format | 全尺寸 (100%) |
| 整合金屬板 | 是的 |
| N鍵無衝功能 | 不 |
| 防鬼鍵 | 不 |
| 金鑰加密 | Cha Cha 20 |
| 響應時間 | 3-5 ms |
| 內部記憶體 | 不 |
| 晶片卡類型 | ISO 7816卡片, ISO 14443A卡片, ISO 14443B卡片, ISO 15693卡片 |
| 作業系統 | Linux, Mac OS, Windows Vista (64位元), Windows XP, Windows XP (64位元), Windows 7, Windows 8, Windows 10, Windows 11 |
| System Requirements-Hardware | USB-A |
| 電纜長度 | 180 cm |
| 產品不含包裝之長度 | 458 mm |
| 產品不含包裝寬度 | 188 mm |
| 產品無包裝高度 | 46 mm |
| 供貨範圍 | 使用手冊, 鍵盤 |
| 背光 | 不 |
| 產品編號 | 佈局 | 產品顏色 | ||
|---|---|---|---|---|

|
JK-A0400BE-2 EAN: 4025112090615 數據表 |
BE (比利時) | 黑色 | |

|
JK-A0400CH-2 EAN: 4025112090516 數據表 |
CH (瑞士) | 黑色 | |

|
JK-A0400DE-2 EAN: 4025112090127 數據表 |
DE (德國) | 黑色 | |

|
JK-A0400ES-2 EAN: 4025112090530 數據表 |
ES (西班牙) | 黑色 | |

|
JK-A0400EU-2 EAN: 4025112090141 數據表 |
EU (美國 + € 符號) | 黑色 | |

|
JK-A0400FR-2 EAN: 4025112090554 數據表 |
FR (法國) | 黑色 | |

|
JK-A0400GB-2 EAN: 4025112090578 數據表 |
GB (英國) | 黑色 | |

|
JK-A0400IT-2 EAN: 4025112090592 數據表 |
IT (義大利) | 黑色 | |

|
JK-A0400PN-2 EAN: 4025112091421 數據表 |
PN (全北歐) | 黑色 | |

|
JK-A0400BE-0 EAN: 4025112090608 數據表 |
BE (比利時) | 灰色 | |

|
JK-A0400CH-0 EAN: 4025112090509 數據表 |
CH (瑞士) | 灰色 | |

|
JK-A0400DE-0 EAN: 4025112090110 數據表 |
DE (德國) | 灰色 | |

|
JK-A0400ES-0 EAN: 4025112090523 數據表 |
ES (西班牙) | 灰色 | |

|
JK-A0400EU-0 EAN: 4025112090134 數據表 |
EU (美國 + € 符號) | 灰色 | |

|
JK-A0400FR-0 EAN: 4025112090547 數據表 |
FR (法國) | 灰色 | |

|
JK-A0400GB-0 EAN: 4025112090561 數據表 |
GB (英國) | 灰色 | |

|
JK-A0400IT-0 EAN: 4025112090585 數據表 |
IT (義大利) | 灰色 | |

|
JK-A0400PN-0 EAN: 4025112094958 數據表 |
PN (全北歐) | 灰色 |


